- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2018 05:48 AM
Hello,
I'm looking for official documentation for integration of Azure AD services and Azure SSO with ServiceNow(Jakarta).
I'm familur with the following thread
Wondering if there is additional information, particularly official ServiceNow documentation on this topic.
Thank you.
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2018 12:18 AM
Hello Dan,
Please find a post from Microsoft site for the integration
Tutorial: Azure Active Directory integration with ServiceNow
In this tutorial, you learn how to integrate ServiceNow with Azure Active Directory (Azure AD).
Integrating ServiceNow with Azure AD provides you with the following benefits:
- You can control in Azure AD who has access to ServiceNow.
- You can enable your users to automatically get signed-on to ServiceNow (Single Sign-On) with their Azure AD accounts.
- You can manage your accounts in one central location - the Azure portal.
If you want to know more details about SaaS app integration with Azure AD, see what is application access and single sign-on with Azure Active Directory.
Prerequisites
To configure Azure AD integration with ServiceNow, you need the following items:
- An Azure AD subscription
- For ServiceNow, an instance or tenant of ServiceNow, Calgary version or higher
- For ServiceNow Express, an instance of ServiceNow Express, Helsinki version or higher
- The ServiceNow tenant must have the Multiple Provider Single Sign On Plugin enabled. This can be done by submitting a service request.
Note
To test the steps in this tutorial, we do not recommend using a production environment.
To test the steps in this tutorial, you should follow these recommendations:
- Do not use your production environment, unless it is necessary.
- If you don't have an Azure AD trial environment, you can get a one-month trial.
Scenario description
In this tutorial, you test Azure AD single sign-on in a test environment. The scenario outlined in this tutorial consists of two main building blocks:
- Adding ServiceNow from the gallery
- Configuring and testing Azure AD single sign-on
Adding ServiceNow from the gallery
To configure the integration of ServiceNow into Azure AD, you need to add ServiceNow from the gallery to your list of managed SaaS apps.
To add ServiceNow from the gallery, perform the following steps:
-
In the Azure portal, on the left navigation panel, click Azure Active Directory icon.

-
Navigate to Enterprise applications. Then go to All applications.

-
To add new application, click New application button on the top of dialog.

-
In the search box, type ServiceNow, select ServiceNow from result panel then click Add button to add the application.

Configure and test Azure AD single sign-on
In this section, you configure and test Azure AD single sign-on with ServiceNow based on a test user called "Britta Simon".
For single sign-on to work, Azure AD needs to know what the counterpart user in ServiceNow is to a user in Azure AD. In other words, a link relationship between an Azure AD user and the related user in ServiceNow needs to be established.
In ServiceNow, assign the value of the user name in Azure AD as the value of the Username to establish the link relationship.
To configure and test Azure AD single sign-on with ServiceNow, you need to complete the following building blocks:
- Configure Azure AD Single Sign-On for ServiceNow - to enable your users to use this feature.
- Configure Azure AD Single Sign-On for ServiceNow Express - to enable your users to use this feature.
- Create an Azure AD test user - to test Azure AD single sign-on with Britta Simon.
- Create a ServiceNow test user - to have a counterpart of Britta Simon in ServiceNow that is linked to the Azure AD representation of user.
- Assign the Azure AD test user - to enable Britta Simon to use Azure AD single sign-on.
- Test single sign-on - to verify whether the configuration works.
Configure Azure AD Single Sign-On for ServiceNow
In this section, you enable Azure AD single sign-on in the Azure portal and configure single sign-on in your ServiceNow application.
To configure Azure AD single sign-on with ServiceNow, perform the following steps:
-
In the Azure portal, on the ServiceNow application integration page, click Single sign-on.

-
On the Single sign-on dialog, select Mode as SAML-based Sign-on to enable single sign-on.

-
On the ServiceNow Domain and URLs section, perform the following steps:

a. In the Sign-on URL textbox, type a URL using the following pattern:
https://<instance-name>.service-now.com/navpage.dob. In the Identifier textbox, type a URL using the following pattern:
https://<instance-name>.service-now.comNote
These values are not real. You'll need to update these values from actual Sign-on URL and Identifier which is explained later in the tutorial.
-
On the SAML Signing Certificate section, click Certificate(Base64) and then save the certificate file on your computer.

-
Click Save button.

-
To generate the Metadata url, perform the following steps:
a. Click App registrations.

b. Click Endpoints to open Endpoints dialog box.

c. Click the copy button to copy FEDERATION METADATA DOCUMENT url and paste it into notepad.

d. Now go to ServiceNow properties and copy the Application ID using Copy button and paste it into notepad.

e. Generate the Metadata URL using the following pattern:
<FEDERATION METADATA DOCUMENT url>?appid=<application id>. Copy the generated value in notepad as this metadata URL will be used later in the tutorial. -
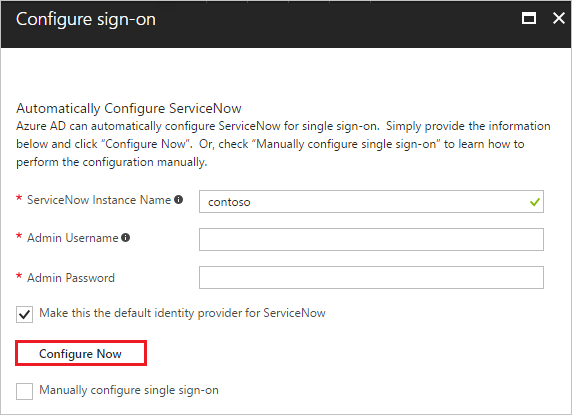
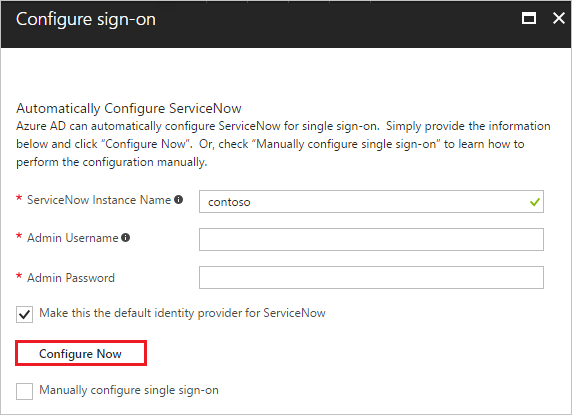
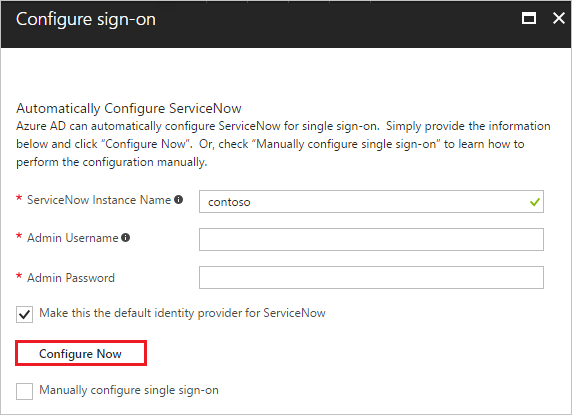
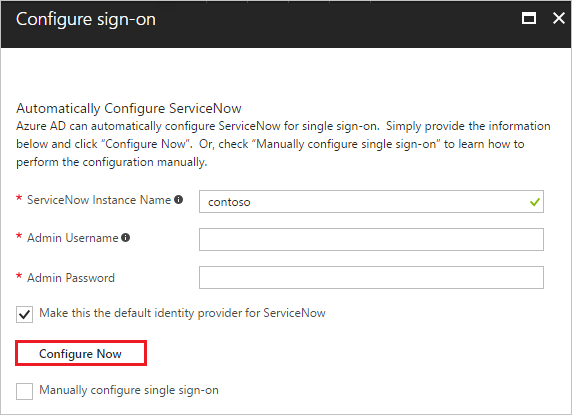
One click configure service is provided for ServiceNow that is, to have Azure AD automatically configure ServiceNow for SAML-based authentication. To enable this service go to ServiceNow Configuration section, click Configure ServiceNowto open Configure sign-on window.

-
Enter your ServiceNow instance name, admin username, and admin password in the Configure sign-on form and click Configure Now. Note that the admin username provided must have the security_admin role assigned in ServiceNow for this to work. Otherwise, to manually configure ServiceNow to use Azure AD as a SAML identity provider, click Manually configure single sign-on and copy the Sign-Out URL, SAML Entity ID, and SAML Single Sign-On Service URL from the Quick Reference section.
-
Sign on to your ServiceNow application as an administrator.
-
Activate the Integration - Multiple Provider Single Sign-On Installer plugin by following the next steps:
a. In the navigation pane on the left side, search System Definition section from the search bar and then click Plugins.

b. Search for Integration - Multiple Provider Single Sign-On Installer.

c. Select the plugin. Right click and select Activate/Upgrade.
d. Click the Activate button.
-
In the navigation pane on the left side, search Multi-Provider SSO section from the search bar and then click Properties.

-
On the Multiple Provider SSO Properties dialog, perform the following steps:

a. As Enable multiple provider SSO, select Yes.
b. As Enable Auto Importing of users from all identity providers into the user table, select Yes.
c. As Enable debug logging for the multiple provider SSO integration, select Yes.
d. In The field on the user table that... textbox, type user_name.
e. Click Save.
-
In the navigation pane on the left side, search Multi-Provider SSO section from the search bar and then click x509 Certificates.

-
On the X.509 Certificates dialog, click New.

-
On the X.509 Certificates dialog, perform the following steps:

a. In the Name textbox, type a name for your configuration (for example: TestSAML2.0).
b. Select Active.
c. As Format, select PEM.
d. As Type, select Trust Store Cert.
e. Open your Base64 encoded certificate downloaded from Azure in notepad, copy the content of it into your clipboard, and then paste it to the PEM Certificate textbox.
f. Click Submit.
-
In the navigation pane on the left side, click Identity Providers.

-
On the Identity Providers dialog, click New.

-
On the Identity Providers dialog, click SAML2 Update1?.

-
On the SAML2 Update1 Properties dialog, perform the following steps:

a. Select URL option in Import Identity Provider Metadata dialogue box.
b. Enter the Metadata URL generated from Azure portal.
c. Click Import.
-
It reads the IdP metadata URL and populates all the fields information.

a. In the Name textbox, type a name for your configuration (for example, SAML 2.0).
b. In the User Field textbox, type email or user_name, depending on which field is used to uniquely identify users in your ServiceNow deployment.
Note
You can configure Azure AD to emit either the Azure AD user ID (user principal name) or the email address as the unique identifier in the SAML token by going to the ServiceNow > Attributes > Single Sign-On section of the Azure portal and mapping the desired field to the nameidentifier attribute. The value stored for the selected attribute in Azure AD (for example, user principal name) must match the value stored in ServiceNow for the entered field (for example, user_name)
c. Copy ServiceNow Homepage value, paste it in the Sign-on URL textbox in ServiceNow Domain and URLs section on Azure portal.
Note
The ServiceNow instance homepage is a concatenation of your ServieNow tenant URL and /navpage.do (for example:
https://fabrikam.service-now.com/navpage.do).d. Copy Entity ID / Issuer value, paste it in Identifier textbox in ServiceNow Domain and URLs section on Azure portal.
e. Under x509 Certificate, lists the certificate you have created in the previous step.
Configure Azure AD Single Sign-On for ServiceNow Express
-
In the Azure portal, on the ServiceNow application integration page, click Single sign-on.

-
On the Single sign-on dialog, select Mode as SAML-based Sign-on to enable single sign-on.

-
On the ServiceNow Domain and URLs section, perform the following steps:

a. In the Sign-on URL textbox, type the value using the following pattern:
https://<instance-name>.service-now.com/navpage.dob. In the Identifier textbox, type a URL using the following pattern:
https://<instance-name>.service-now.comNote
These values are not real. Update these values with the actual Sign-on URL and Identifier. Contact ServiceNow Client support team to get these values.
-
On the SAML Signing Certificate section, click Certificate(Base64) and then save the certificate file on your computer.

-
Click Save button.

-
One click configure service is provided for ServiceNow that is, to have Azure AD automatically configure ServiceNow for SAML-based authentication. To enable this service go to ServiceNow Configuration section, click Configure ServiceNowto open Configure sign-on window.

-
Enter your ServiceNow instance name, admin username, and admin password in the Configure sign-on form and click Configure Now. Note that the admin username provided must have the security_admin role assigned in ServiceNow for this to work. Otherwise, to manually configure ServiceNow to use Azure AD as a SAML identity provider, click Manually configure single sign-on and copy the Sign-Out URL, SAML Entity ID, and SAML Single Sign-On Service URL from the Quick Reference section.
-
Sign on to your ServiceNow Express application as an administrator.
-
In the navigation pane on the left side, click Single Sign-On.

-
On the Single Sign-On dialog, click the configuration icon on the upper right and set the following properties:

a. Toggle Enable multiple provider SSO to the right.
b. Toggle Enable debug logging for the multiple provider SSO integration to the right.
c. In The field on the user table that... textbox, type user_name.
-
On the Single Sign-On dialog, click Add New Certificate.

-
On the X.509 Certificates dialog, perform the following steps:

a. In the Name textbox, type a name for your configuration (for example: TestSAML2.0).
b. Select Active.
c. As Format, select PEM.
d. As Type, select Trust Store Cert.
e. Open your Base64 encoded certificate downloaded from Azure portal in notepad, copy the content of it into your clipboard, and then paste it to the PEM Certificate textbox.
f. Click Update
-
On the Single Sign-On dialog, click Add New IdP.

-
On the Add New Identity Provider dialog, under Configure Identity Provider, perform the following steps:

a. In the Name textbox, type a name for your configuration (for example: SAML 2.0).
b. In the Identity Provider URL field, paste the value of Identity Provider ID which you have copied from Azure portal.
c. In the Identity Provider's AuthnRequest field, paste the value of Authentication Request URL which you have copied from Azure portal.
d. In the Identity Provider's SingleLogoutRequest field, paste the value of Single Sign-Out Service URL which you have copied from Azure portal
e. As Identity Provider Certificate, select the certificate you have created in the previous step.
-
Click Advanced Settings, and under Additional Identity Provider Properties, perform the following steps:

a. In the Protocol Binding for the IDP's SingleLogoutRequest textbox, type urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect.
b. In the NameID Policy textbox, type urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified.
c. In the AuthnContextClassRef Method, type
http://schemas.microsoft.com/ws/2008/06/identity/authenticationmethod/password.d. Deselect Create an AuthnContextClass.
-
Under Additional Service Provider Properties, perform the following steps:

a. In the ServiceNow Homepage textbox, type the URL of your ServiceNow instance homepage.
Note
The ServiceNow instance homepage is a concatenation of your ServieNow tenant URL and /navpage.do (for example:
https://fabrikam.service-now.com/navpage.do).b. In the Entity ID / Issuer textbox, type the URL of your ServiceNow tenant.
c. In the Audience URI textbox, type the URL of your ServiceNow tenant.
d. In Clock Skew textbox, type 60.
e. In the User Field textbox, type email or user_name, depending on which field is used to uniquely identify users in your ServiceNow deployment.
Note
You can configure Azure AD to emit either the Azure AD user ID (user principal name) or the email address as the unique identifier in the SAML token by going to the ServiceNow > Attributes > Single Sign-On section of the Azure portal and mapping the desired field to the nameidentifier attribute. The value stored for the selected attribute in Azure AD (for example, user principal name) must match the value stored in ServiceNow for the entered field (for example, user_name)
f. Click Save.
Tip
You can now read a concise version of these instructions inside the Azure portal, while you are setting up the app! After adding this app from the Active Directory > Enterprise Applications section, simply click the Single Sign-On tab and access the embedded documentation through the Configuration section at the bottom. You can read more about the embedded documentation feature here: Azure AD embedded documentation
Create an Azure AD test user
The objective of this section is to create a test user in the Azure portal called Britta Simon.

To create a test user in Azure AD, perform the following steps:
-
In the Azure portal, in the left pane, click the Azure Active Directory button.

-
To display the list of users, go to Users and groups, and then click All users.

-
To open the User dialog box, click Add at the top of the All Users dialog box.

-
In the User dialog box, perform the following steps:

a. In the Name box, type BrittaSimon.
b. In the User name box, type the email address of user Britta Simon.
c. Select the Show Password check box, and then write down the value that's displayed in the Password box.
d. Click Create.
Create a ServiceNow test user
In this section, you create a user called Britta Simon in ServiceNow. If you don't know how to add a user in your ServiceNow or ServiceNow Express account, contact ServiceNow Client support team
Assign the Azure AD test user
In this section, you enable Britta Simon to use Azure single sign-on by granting access to ServiceNow.

To assign Britta Simon to ServiceNow, perform the following steps:
-
In the Azure portal, open the applications view, and then navigate to the directory view and go to Enterprise applicationsthen click All applications.

-
In the applications list, select ServiceNow.

-
In the menu on the left, click Users and groups.

-
Click Add button. Then select Users and groups on Add Assignment dialog.

-
On Users and groups dialog, select Britta Simon in the Users list.
-
Click Select button on Users and groups dialog.
-
Click Assign button on Add Assignment dialog.
Test single sign-on
In this section, you test your Azure AD single sign-on configuration using the Access Panel.
When you click the ServiceNow tile in the Access Panel, you should get automatically signed-on to your ServiceNow application. For more information about the Access Panel, see Introduction to the Access Panel.
Thanks,
Dravvy
Please Hit like, Helpful or Correct depending on the impact of the response
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2018 12:18 AM
Hello Dan,
Please find a post from Microsoft site for the integration
Tutorial: Azure Active Directory integration with ServiceNow
In this tutorial, you learn how to integrate ServiceNow with Azure Active Directory (Azure AD).
Integrating ServiceNow with Azure AD provides you with the following benefits:
- You can control in Azure AD who has access to ServiceNow.
- You can enable your users to automatically get signed-on to ServiceNow (Single Sign-On) with their Azure AD accounts.
- You can manage your accounts in one central location - the Azure portal.
If you want to know more details about SaaS app integration with Azure AD, see what is application access and single sign-on with Azure Active Directory.
Prerequisites
To configure Azure AD integration with ServiceNow, you need the following items:
- An Azure AD subscription
- For ServiceNow, an instance or tenant of ServiceNow, Calgary version or higher
- For ServiceNow Express, an instance of ServiceNow Express, Helsinki version or higher
- The ServiceNow tenant must have the Multiple Provider Single Sign On Plugin enabled. This can be done by submitting a service request.
Note
To test the steps in this tutorial, we do not recommend using a production environment.
To test the steps in this tutorial, you should follow these recommendations:
- Do not use your production environment, unless it is necessary.
- If you don't have an Azure AD trial environment, you can get a one-month trial.
Scenario description
In this tutorial, you test Azure AD single sign-on in a test environment. The scenario outlined in this tutorial consists of two main building blocks:
- Adding ServiceNow from the gallery
- Configuring and testing Azure AD single sign-on
Adding ServiceNow from the gallery
To configure the integration of ServiceNow into Azure AD, you need to add ServiceNow from the gallery to your list of managed SaaS apps.
To add ServiceNow from the gallery, perform the following steps:
-
In the Azure portal, on the left navigation panel, click Azure Active Directory icon.

-
Navigate to Enterprise applications. Then go to All applications.

-
To add new application, click New application button on the top of dialog.

-
In the search box, type ServiceNow, select ServiceNow from result panel then click Add button to add the application.

Configure and test Azure AD single sign-on
In this section, you configure and test Azure AD single sign-on with ServiceNow based on a test user called "Britta Simon".
For single sign-on to work, Azure AD needs to know what the counterpart user in ServiceNow is to a user in Azure AD. In other words, a link relationship between an Azure AD user and the related user in ServiceNow needs to be established.
In ServiceNow, assign the value of the user name in Azure AD as the value of the Username to establish the link relationship.
To configure and test Azure AD single sign-on with ServiceNow, you need to complete the following building blocks:
- Configure Azure AD Single Sign-On for ServiceNow - to enable your users to use this feature.
- Configure Azure AD Single Sign-On for ServiceNow Express - to enable your users to use this feature.
- Create an Azure AD test user - to test Azure AD single sign-on with Britta Simon.
- Create a ServiceNow test user - to have a counterpart of Britta Simon in ServiceNow that is linked to the Azure AD representation of user.
- Assign the Azure AD test user - to enable Britta Simon to use Azure AD single sign-on.
- Test single sign-on - to verify whether the configuration works.
Configure Azure AD Single Sign-On for ServiceNow
In this section, you enable Azure AD single sign-on in the Azure portal and configure single sign-on in your ServiceNow application.
To configure Azure AD single sign-on with ServiceNow, perform the following steps:
-
In the Azure portal, on the ServiceNow application integration page, click Single sign-on.

-
On the Single sign-on dialog, select Mode as SAML-based Sign-on to enable single sign-on.

-
On the ServiceNow Domain and URLs section, perform the following steps:

a. In the Sign-on URL textbox, type a URL using the following pattern:
https://<instance-name>.service-now.com/navpage.dob. In the Identifier textbox, type a URL using the following pattern:
https://<instance-name>.service-now.comNote
These values are not real. You'll need to update these values from actual Sign-on URL and Identifier which is explained later in the tutorial.
-
On the SAML Signing Certificate section, click Certificate(Base64) and then save the certificate file on your computer.

-
Click Save button.

-
To generate the Metadata url, perform the following steps:
a. Click App registrations.

b. Click Endpoints to open Endpoints dialog box.

c. Click the copy button to copy FEDERATION METADATA DOCUMENT url and paste it into notepad.

d. Now go to ServiceNow properties and copy the Application ID using Copy button and paste it into notepad.

e. Generate the Metadata URL using the following pattern:
<FEDERATION METADATA DOCUMENT url>?appid=<application id>. Copy the generated value in notepad as this metadata URL will be used later in the tutorial. -
One click configure service is provided for ServiceNow that is, to have Azure AD automatically configure ServiceNow for SAML-based authentication. To enable this service go to ServiceNow Configuration section, click Configure ServiceNowto open Configure sign-on window.

-
Enter your ServiceNow instance name, admin username, and admin password in the Configure sign-on form and click Configure Now. Note that the admin username provided must have the security_admin role assigned in ServiceNow for this to work. Otherwise, to manually configure ServiceNow to use Azure AD as a SAML identity provider, click Manually configure single sign-on and copy the Sign-Out URL, SAML Entity ID, and SAML Single Sign-On Service URL from the Quick Reference section.
-
Sign on to your ServiceNow application as an administrator.
-
Activate the Integration - Multiple Provider Single Sign-On Installer plugin by following the next steps:
a. In the navigation pane on the left side, search System Definition section from the search bar and then click Plugins.

b. Search for Integration - Multiple Provider Single Sign-On Installer.

c. Select the plugin. Right click and select Activate/Upgrade.
d. Click the Activate button.
-
In the navigation pane on the left side, search Multi-Provider SSO section from the search bar and then click Properties.

-
On the Multiple Provider SSO Properties dialog, perform the following steps:

a. As Enable multiple provider SSO, select Yes.
b. As Enable Auto Importing of users from all identity providers into the user table, select Yes.
c. As Enable debug logging for the multiple provider SSO integration, select Yes.
d. In The field on the user table that... textbox, type user_name.
e. Click Save.
-
In the navigation pane on the left side, search Multi-Provider SSO section from the search bar and then click x509 Certificates.

-
On the X.509 Certificates dialog, click New.

-
On the X.509 Certificates dialog, perform the following steps:

a. In the Name textbox, type a name for your configuration (for example: TestSAML2.0).
b. Select Active.
c. As Format, select PEM.
d. As Type, select Trust Store Cert.
e. Open your Base64 encoded certificate downloaded from Azure in notepad, copy the content of it into your clipboard, and then paste it to the PEM Certificate textbox.
f. Click Submit.
-
In the navigation pane on the left side, click Identity Providers.

-
On the Identity Providers dialog, click New.

-
On the Identity Providers dialog, click SAML2 Update1?.

-
On the SAML2 Update1 Properties dialog, perform the following steps:

a. Select URL option in Import Identity Provider Metadata dialogue box.
b. Enter the Metadata URL generated from Azure portal.
c. Click Import.
-
It reads the IdP metadata URL and populates all the fields information.

a. In the Name textbox, type a name for your configuration (for example, SAML 2.0).
b. In the User Field textbox, type email or user_name, depending on which field is used to uniquely identify users in your ServiceNow deployment.
Note
You can configure Azure AD to emit either the Azure AD user ID (user principal name) or the email address as the unique identifier in the SAML token by going to the ServiceNow > Attributes > Single Sign-On section of the Azure portal and mapping the desired field to the nameidentifier attribute. The value stored for the selected attribute in Azure AD (for example, user principal name) must match the value stored in ServiceNow for the entered field (for example, user_name)
c. Copy ServiceNow Homepage value, paste it in the Sign-on URL textbox in ServiceNow Domain and URLs section on Azure portal.
Note
The ServiceNow instance homepage is a concatenation of your ServieNow tenant URL and /navpage.do (for example:
https://fabrikam.service-now.com/navpage.do).d. Copy Entity ID / Issuer value, paste it in Identifier textbox in ServiceNow Domain and URLs section on Azure portal.
e. Under x509 Certificate, lists the certificate you have created in the previous step.
Configure Azure AD Single Sign-On for ServiceNow Express
-
In the Azure portal, on the ServiceNow application integration page, click Single sign-on.

-
On the Single sign-on dialog, select Mode as SAML-based Sign-on to enable single sign-on.

-
On the ServiceNow Domain and URLs section, perform the following steps:

a. In the Sign-on URL textbox, type the value using the following pattern:
https://<instance-name>.service-now.com/navpage.dob. In the Identifier textbox, type a URL using the following pattern:
https://<instance-name>.service-now.comNote
These values are not real. Update these values with the actual Sign-on URL and Identifier. Contact ServiceNow Client support team to get these values.
-
On the SAML Signing Certificate section, click Certificate(Base64) and then save the certificate file on your computer.

-
Click Save button.

-
One click configure service is provided for ServiceNow that is, to have Azure AD automatically configure ServiceNow for SAML-based authentication. To enable this service go to ServiceNow Configuration section, click Configure ServiceNowto open Configure sign-on window.

-
Enter your ServiceNow instance name, admin username, and admin password in the Configure sign-on form and click Configure Now. Note that the admin username provided must have the security_admin role assigned in ServiceNow for this to work. Otherwise, to manually configure ServiceNow to use Azure AD as a SAML identity provider, click Manually configure single sign-on and copy the Sign-Out URL, SAML Entity ID, and SAML Single Sign-On Service URL from the Quick Reference section.
-
Sign on to your ServiceNow Express application as an administrator.
-
In the navigation pane on the left side, click Single Sign-On.

-
On the Single Sign-On dialog, click the configuration icon on the upper right and set the following properties:

a. Toggle Enable multiple provider SSO to the right.
b. Toggle Enable debug logging for the multiple provider SSO integration to the right.
c. In The field on the user table that... textbox, type user_name.
-
On the Single Sign-On dialog, click Add New Certificate.

-
On the X.509 Certificates dialog, perform the following steps:

a. In the Name textbox, type a name for your configuration (for example: TestSAML2.0).
b. Select Active.
c. As Format, select PEM.
d. As Type, select Trust Store Cert.
e. Open your Base64 encoded certificate downloaded from Azure portal in notepad, copy the content of it into your clipboard, and then paste it to the PEM Certificate textbox.
f. Click Update
-
On the Single Sign-On dialog, click Add New IdP.

-
On the Add New Identity Provider dialog, under Configure Identity Provider, perform the following steps:

a. In the Name textbox, type a name for your configuration (for example: SAML 2.0).
b. In the Identity Provider URL field, paste the value of Identity Provider ID which you have copied from Azure portal.
c. In the Identity Provider's AuthnRequest field, paste the value of Authentication Request URL which you have copied from Azure portal.
d. In the Identity Provider's SingleLogoutRequest field, paste the value of Single Sign-Out Service URL which you have copied from Azure portal
e. As Identity Provider Certificate, select the certificate you have created in the previous step.
-
Click Advanced Settings, and under Additional Identity Provider Properties, perform the following steps:

a. In the Protocol Binding for the IDP's SingleLogoutRequest textbox, type urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect.
b. In the NameID Policy textbox, type urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified.
c. In the AuthnContextClassRef Method, type
http://schemas.microsoft.com/ws/2008/06/identity/authenticationmethod/password.d. Deselect Create an AuthnContextClass.
-
Under Additional Service Provider Properties, perform the following steps:

a. In the ServiceNow Homepage textbox, type the URL of your ServiceNow instance homepage.
Note
The ServiceNow instance homepage is a concatenation of your ServieNow tenant URL and /navpage.do (for example:
https://fabrikam.service-now.com/navpage.do).b. In the Entity ID / Issuer textbox, type the URL of your ServiceNow tenant.
c. In the Audience URI textbox, type the URL of your ServiceNow tenant.
d. In Clock Skew textbox, type 60.
e. In the User Field textbox, type email or user_name, depending on which field is used to uniquely identify users in your ServiceNow deployment.
Note
You can configure Azure AD to emit either the Azure AD user ID (user principal name) or the email address as the unique identifier in the SAML token by going to the ServiceNow > Attributes > Single Sign-On section of the Azure portal and mapping the desired field to the nameidentifier attribute. The value stored for the selected attribute in Azure AD (for example, user principal name) must match the value stored in ServiceNow for the entered field (for example, user_name)
f. Click Save.
Tip
You can now read a concise version of these instructions inside the Azure portal, while you are setting up the app! After adding this app from the Active Directory > Enterprise Applications section, simply click the Single Sign-On tab and access the embedded documentation through the Configuration section at the bottom. You can read more about the embedded documentation feature here: Azure AD embedded documentation
Create an Azure AD test user
The objective of this section is to create a test user in the Azure portal called Britta Simon.

To create a test user in Azure AD, perform the following steps:
-
In the Azure portal, in the left pane, click the Azure Active Directory button.

-
To display the list of users, go to Users and groups, and then click All users.

-
To open the User dialog box, click Add at the top of the All Users dialog box.

-
In the User dialog box, perform the following steps:

a. In the Name box, type BrittaSimon.
b. In the User name box, type the email address of user Britta Simon.
c. Select the Show Password check box, and then write down the value that's displayed in the Password box.
d. Click Create.
Create a ServiceNow test user
In this section, you create a user called Britta Simon in ServiceNow. If you don't know how to add a user in your ServiceNow or ServiceNow Express account, contact ServiceNow Client support team
Assign the Azure AD test user
In this section, you enable Britta Simon to use Azure single sign-on by granting access to ServiceNow.

To assign Britta Simon to ServiceNow, perform the following steps:
-
In the Azure portal, open the applications view, and then navigate to the directory view and go to Enterprise applicationsthen click All applications.

-
In the applications list, select ServiceNow.

-
In the menu on the left, click Users and groups.

-
Click Add button. Then select Users and groups on Add Assignment dialog.

-
On Users and groups dialog, select Britta Simon in the Users list.
-
Click Select button on Users and groups dialog.
-
Click Assign button on Add Assignment dialog.
Test single sign-on
In this section, you test your Azure AD single sign-on configuration using the Access Panel.
When you click the ServiceNow tile in the Access Panel, you should get automatically signed-on to your ServiceNow application. For more information about the Access Panel, see Introduction to the Access Panel.
Thanks,
Dravvy
Please Hit like, Helpful or Correct depending on the impact of the response
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2018 04:05 AM
Yes, thats exactly what i was looking for, Thank you so much Dravvy!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-19-2018 04:12 AM
That great.
Feel free to mark it as helpful 🙂
Regards,
Dravvy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-04-2019 05:58 AM
Hi Guys,
I have followed that guide several times but im still unable to integrate Service Now (Dev environment) with SSO (Azure).
Im getting stuck in the step where I have to login as a Service Now Admin (with Security Admin role) and it keeps telling me "The user you specified is not authorized to perform this operation".
I have also tried configuring this Manually but the steps shown on the portal do not match several of the steps that I have to complete in Service Now.
Service Now version: Jakarta
Help or guidance are greatly appreciated ( :
Thanks,
Lennart

